Ransomware is on the rise – protect your business
What are the rising ransomware threats that businesses of all sizes face today? How can you protect your data, people, and productivity from these threats? We’re here to give you the answers about the latest rising ransomware threats.
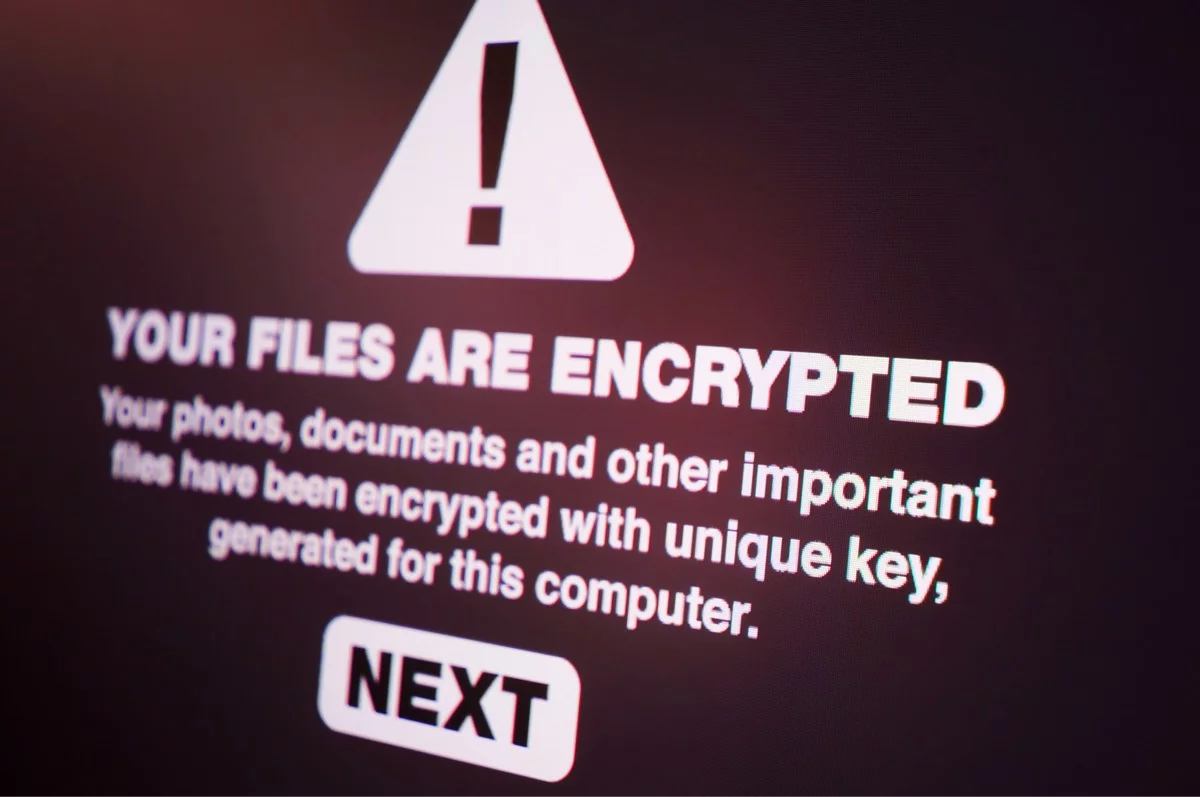
Ransomware is a type of malware (malicious software) that prevents you from accessing your computer or the data that’s stored on it. As a result, your computer may become locked, or the data on it might be stolen, deleted or encrypted so it can be held for ransom.
Unfortunately, attacks are growing in number and scale in 2021 as millions of people across the country work or attend school remotely. In some cases, these remote workers and learners inadvertently open ‘back doors’ to networks because their devices are not protected by corporate or institutional security measures.
Many businesses and organisations in the UK are very much aware of the threat of malware. In fact, the average business now devotes more than a fifth of its IT budget to cybersecurity. But the fact is, ransomware is constantly evolving to counter any efforts to thwart it, and businesses are now under siege from more attacks than ever before. So it pays to stay aware of the latest threats.
90% of companies in the UK will experience some kind of downtime due to malware, which typically results in loss of data, security, productivity, and revenue.
Protecting against ransomware is a crucial aspect of business continuity – the planning and preparation that keeps you operational in the face of otherwise devastating issues like ransomware.
In this article, we look at some of the ransomware threats that exist today and how you can protect your business from them. We also talk about how a solid backup strategy and disaster recovery plan can mitigate these and other risks should the worst-case scenario happen.
What is ransomware?
Ransomware is one of the most serious kinds of cybercrime that organisations face today. Ransomware is a kind of malicious software – malware – that encrypts files and documents on anything from a single computer, all the way up to an entire network, including servers.
How could ransomware infect my business?
Many ransomware infections start with someone inside an organisation clicking on what looks like an innocent attachment that, when opened, downloads the malicious payload and encrypts the network.
Other, larger ransomware campaigns use flaws in popular business software, weak passwords, and other vulnerabilities to gain access to organisations. They target weak points like servers connected to the internet or remote desktop logins. Attackers can then search through the network, attempting to control as much as possible before encrypting as much data and as many systems as they possibly can.
The Covid-19 pandemic has increased the number of larger ransomware campaigns as remote working forces businesses and their staff to use certain tools and technologies criminals can exploit:
- Mobile devices
- Remote desktop tools
- Virtual Private Networks (VPNs)
- Public WiFi hotspots
- Cloud-based tools with poor password management
- Phishing attacks promising information about the virus or vaccinations
What kind of businesses get attacked by ransomware?
Any business that uses the internet and email communications is vulnerable and must take action to protect itself. However, organisations in these industries are targeted more than most:
- Government
- Education
- Services
- Manufacturing
- Technology
- Healthcare
- Retail
Manufacturing companies are the most likely targets of double-extortion ransomware attacks, according to a recent report from ThreatLabZ. In a double-extortion attack, criminals not only encrypt data but steal it too, enabling them to blackmail victims into preventing its publication.
How could ransomware affect my businesses?
Depending on the severity of the ransomware infection, your business could be mildly affected and able to carry on with business more or less as usual. Or your entire operation could be on hold until the problem is fixed.
Imagine if your business-critical files and documents, networks or servers are suddenly encrypted and completely inaccessible. Not a pleasant scenario. Even worse if you must pay a considerable sum of money to cybercriminals to get access again.
Outside of the immediate impact ransomware can have on a network, it can result in an ongoing financial hit if you cannot provide your usual services to customers.
Market research [5] has indicated that ransomware attacks cost UK businesses £346 million per annum
There is also the impact on your reputation to worry about too. In some industries, the fact you’ve fallen victim to a cyberattack could potentially drive customers away permanently.
How would I deal with a ransomware infection?
Victims of ransomware can often be left with few choices. They can regain access to their encrypted network by paying a ransom to the criminals behind the ransomware or try to restore from backups.
In some cases, there is a decryption key freely available that can be used to decrypt the computer. The No More Ransom website was created by Europol and the Dutch National Police in collaboration with a number of cybersecurity companies, including Kaspersky Lab and McAfee. It offers free decryption tools for ransomware variants to help victims retrieve their encrypted data.
There is also the rather daunting option of starting again from scratch!
How long does it take to recover from a ransomware infection?
While it is possible to regain some operations in the short term after the ransomware infection has been dealt with, many affected organisations struggle to get all systems back up and running until months after the incident.
What ransomware threats are out there in 2021?
EternalBlue network vulnerability
EternalBlue is a network vulnerability that powered WannaCry and NotPetya. This is still one of the most common exploits used to spread attacks – despite the fact that the security patch to protect against it has been available for over three years.
Maze ransomware
Maze ransomware is malware that targets organisations worldwide across many industries. Standard attack methodologies used by the Maze ransomware include guessing default/weak passwords or spear-phishing through a targeted mail with a .docx attachment containing a malicious macro.
Once an initial machine in the network is compromised, the malware starts scanning the network to find vulnerabilities. The malware scans various facets like network configurations and various Active Directory attributes such as permissions, accounts, and domain trusts.
REvil and Sodinokibi ransomware
REvil is a file encryption virus that encrypts all the files and demands money from the victim once it infiltrates the system. Then cybercriminals force victims to pay the ransom using bitcoins. If the victim does not pay the ransom within a specific time period, the ransom rate doubles.
The delivery of REvil and the initial infection vectors vary, but they have been known to include phishing.
Sodinokibi ransomware is a type of REvil ransomware that first started spreading in 2019 but continues to spread through software installers with remote desktop servers and other backdoor vulnerabilities.
Ragnar Locker ransomware
Ragnar Locker is ransomware that affects devices running Microsoft Windows operating systems. It was initially observed towards the end of December 2019 as part of a series of attacks against compromised networks.
This malware is generally deployed manually after an initial compromise by other means. Attacked deploy it after first collecting sensitive data from infected machines and uploading it to their servers. Victims are notified that the files containing the sensitive data will be released to the public if a ransom is not paid.
…and many others
This is not a comprehensive list but it does include some of the most effective ransomware deployed by cybercriminals in the last year or so. There are many other kinds of ransomware out there. Unfortunately, businesses will come under attack from new, malicious creations in the future too.
How you can protect your business from ransomware
Staying one step ahead in today’s threat landscape requires an awareness of emerging attack strategies and taking appropriate steps to provide an adequate defence.
Limit connections to the internet
With large numbers of ransomware attacks starting with hackers exploiting insecure internet-facing ports and remote desktop protocols, one of the key things an organisation can do to prevent itself from falling victim is by ensuring ports aren’t exposed to the internet if they don’t need to be.
When remote ports are necessary, organisations should ensure that the login credentials have a complex password to protect against criminals looking to deploy ransomware from being able to crack simple passwords using brute force attacks as a way in. Applying two-factor authentication to these accounts can also act as a barrier to attacks, as there will be an alert if there’s any attempt at unauthorised access.
Firewall
Attackers target centralised resources like major on-premise systems because this is where the most valuable information is stored. And the most valuable information warrants the highest ransom payments.
You need a firewall capable of protecting all of your central applications. For example, an effective Web Application Firewall (WAF) will ensure that every cloud resource is well protected.
Patch vulnerabilities immediately
A patch is a set of changes to a computer program, an app, or its supporting data designed to update, fix, or improve it. This includes fixing security vulnerabilities that can be exploited by criminals to infect a machine or entire networks.
It is vital in terms of protecting your business from ransomware that you can stay aware of when a patch becomes available and can deploy it in a fast but controlled manner.
A Managed IT Support service will keep your systems and devices up-to-date, protected, patched, and secure, helping you avoid unplanned downtime, security breaches, and unexpected costs to fix issues and recover data.
Keep software up-to-date
A vital part of securing your business is to ensure all internet-facing software is kept up-to-date. Whether you automatically install updates as they become available or need to make manual updates will depend on the software itself. But keeping desktop applications, mobile apps, and website software updated will save you potential heartache and costly ransomware infections in the future.
Vulnerability scanning
Vulnerability scanning can help businesses audit the safety of their existing systems and detect potential malicious code or files that have already been injected onto systems. Once identified, they can be safely quarantined.
Enable multifactor authentication (MFA) everywhere possible
As the name suggests, multifactor authentication (MFA) provides multiple layers of security and protection from attempts to access an account.
User accounts for cloud-hosted tools and file systems like Google Drive or Dropbox should always be protected by 2-factor authentication.
Ensure only secure passwords are used throughout your business
The use of strong passwords is an essential part of protecting the security and identity of your business and its employees. Passwords are the weak point in systems and websites that cybercriminals actively target.
Poor password management, especially in these days of remote working, presents an additional risk factor – and attackers are taking full advantage.
Our article, Ultimate guide to password security, provides detailed information on creating secure passwords in your business.
Provide training for your staff
We always recommend that every company provides mandatory cybersecurity awareness training for any employee. This should provide information about security threats and the steps individuals should take to secure their devices:
- Password security
- Spotting suspicious links in emails, texts and on social media
- Using public WiFi for portable devices
- Safe web browsing
- Safe file sharing
- Online meeting security and privacy
- Avoiding tech support scams
When it comes to stopping phishing attacks, you should provide employees with training on spotting an incoming malware attack. It’s vital that people know what to look out for and can spot the subtle indicators that may prevent an attack on your business like these:
- Poor formatting
- Spelling mistakes
- Obscure email addresses (for example, an email purporting to be from ‘Microsoft Security’ that is sent from an obscure email address that doesn’t even contain the word Microsoft)
This is an ideal forum to take employees through your security policies and what to do in the event of a breach.
Join the Cyber Essentials scheme
Cyber Essentials is a government-run scheme designed to help British organisations of any size protect themselves against common business threats. It identifies technical security controls that an organisation needs to have in place.
Learn more about Cyber Essentials on the National Cyber Security Centre website.
Create (and test) a disaster recovery plan
Should the worst-case scenario happen and your business is struck by a ransomware infection, you need to get your business back up and running as quickly as possible. A disaster recovery plan allows you to document and execute a pre-planned list of actions to backup and restore your critical data without any data loss.
It’s essential to put your recovery plan to the test. Testing your disaster recovery process means undertaking a full system restore, including applications and operating systems, to ensure your backup and recovery process is viable.
Knowing your data is backed up and that those backups are good-to-go, ready for an emergency recovery to get you back up and running will bring considerable peace of mind.
Another of our articles, Free guide to data backup and disaster recovery, provides detailed information on how a good backup strategy and disaster recovery plan can mitigate risks like ransomware.
Need support protecting your business from ransomware and other threats?
We help businesses and organisations across Scotland to stay aware of ransomware and other threats to data security and business continuity. Our Managed IT support service keeps them protected 24/7 from constantly evolving threats like ransomware. It also includes complete monitoring and alert coverage too.
Combine Managed IT support with our Disaster Recovery service to ensure you can recover from significant issues rapidly and without data loss, helping you get back to business as usual with minimal downtime. All from a single supplier at a cost-effective monthly payment
Contact us today to begin the conversation about your IT requirements.




